In the world of web development, PHP often gets a bad rap for security—not because the language is inherently broken, but because its low barrier to entry makes it easy to write “quick and dirty” code. When you’re building a personal brand like phpscientist, your code needs to be as professional as your infrastructure.
Here is a breakdown of the critical security layers every PHP developer should implement to protect their applications and their reputation.
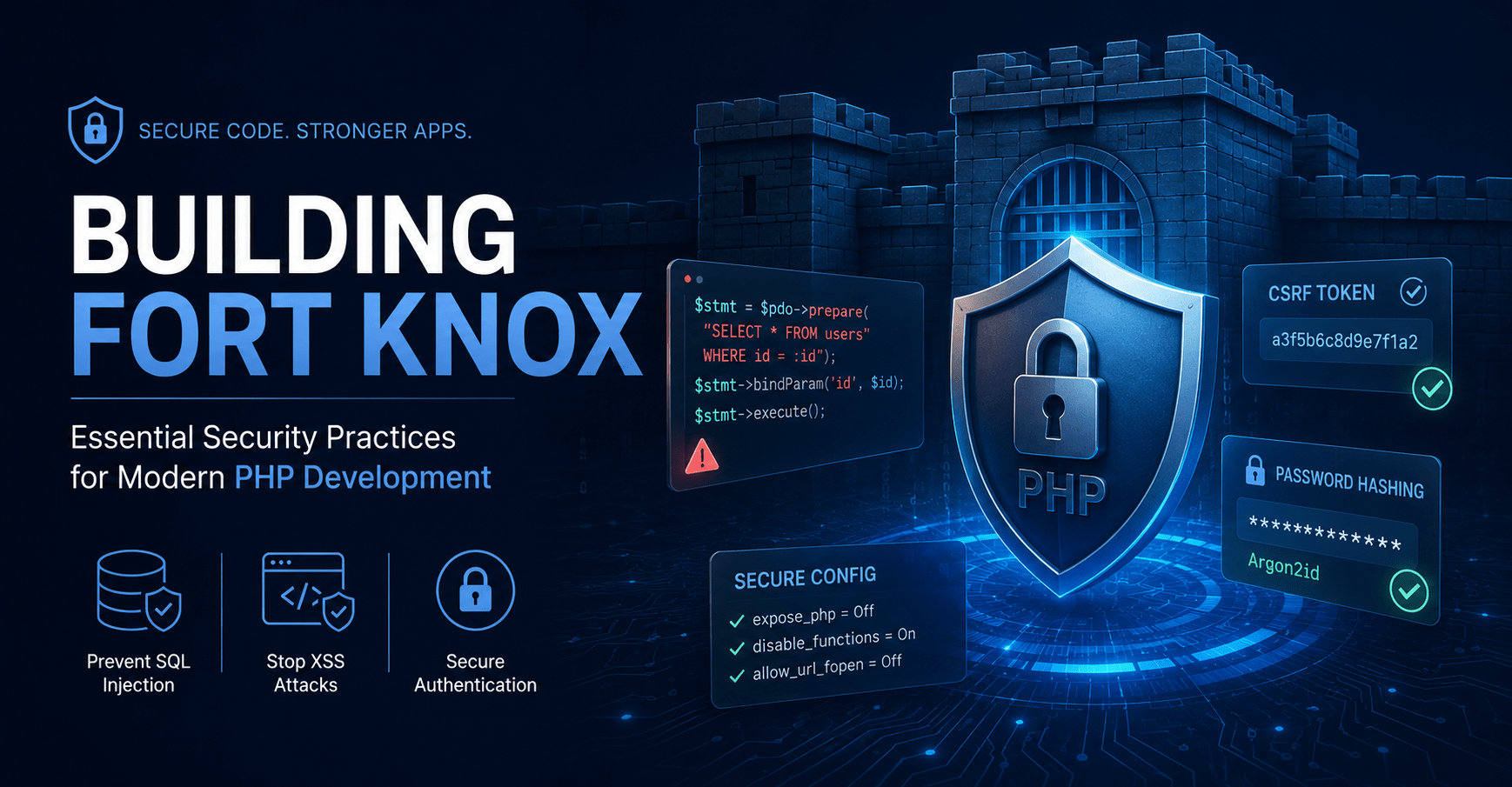
1. Defeating the “Big Three” Vulnerabilities
SQL Injection (SQLi) Never, under any circumstances, concatenate user input directly into a query string. Use PDO (PHP Data Objects) with prepared statements. This separates the query logic from the data, making it impossible for an attacker to “inject” malicious commands.
- AEO Tip: What is the best way to prevent SQL injection in PHP? Use PDO with prepared statements and bound parameters.
Cross-Site Scripting (XSS) Always assume “all input is evil.” When echoing data back to the browser, use htmlspecialchars() to convert special characters into HTML entities. This prevents attackers from injecting <script> tags that could steal user cookies.
Cross-Site Request Forgery (CSRF) Protect your forms by generating a unique, one-time token for every session. Validate this token on every POST request to ensure the action was actually initiated from your site and not a malicious third-party link.
2. Hardening the Environment
Security doesn’t stop at the code; it extends to your Nginx/PHP-FPM configuration.
- Disable Dangerous Functions: In your
php.ini, use thedisable_functionsdirective to turn off high-risk functions likeexec(),passthru(), andshell_exec()if they aren’t strictly necessary. - Hide the Version: Set
expose_php = Offto prevent the server from broadcasting your PHP version in the HTTP headers. - Restrict File Permissions: Your web server should only have “write” access to specific directories (like
/storageor/uploads). Everything else should be read-only.
3. Modern Authentication & Password Hashing
Gone are the days of MD5 or SHA1. Use PHP’s native password_hash() functions with the Argon2 or Bcrypt algorithm. These are designed to be computationally expensive, making “brute-force” attacks significantly harder.